A stolen laptop isn’t just the loss of a screen and keyboard. It’s potentially the loss of everything it contains — and your insurance won’t cover that.
Every week in Ireland, hundreds of laptops are stolen from business premises. Insurance covers the hardware, you buy a new device, and move on. This is exactly the reflex that turns a simple company laptop theft into a ticking time bomb for your data and GDPR compliance. Here’s why this risk is underestimated — and how well-designed IT security for SMEs in Dublin anticipates it.
What a business laptop actually contains
Ask yourself seriously: what does one of your employees’ computers really contain?
- Saved login credentials in the browser (email, ERP, business tools)
- Locally downloaded files — quotes, contracts, client lists
- Access to professional email, often without two-factor authentication
- Personal data of clients or employees covered by GDPR
- Sometimes, an active VPN connection to your internal network
An unencrypted computer is an open key to your entire information system. No hacking skills required: a bootable USB drive is enough, and all company data becomes accessible within minutes.

The consequences SMEs underestimate after a laptop theft
72h
To notify the DPC after a personal data breach
4%
Of annual turnover — GDPR fine ceiling
4–8h
To reconfigure an undocumented workstation
1. The GDPR notification obligation
If the stolen data contains personal information — and this is almost always the case — you have 72 hours to notify the Data Protection Commission (DPC). In the event of a confirmed breach, fines can reach 4% of annual turnover. For an SME in Dublin or across Ireland, this is a potentially fatal data risk.
2. The rebound risk: your network exposed
If the laptop had an active VPN connection or saved credentials to your cloud tools, the thief can access your network weeks after the theft. A company laptop theft becomes a prolonged cyber intrusion.
3. The immediate operational impact
Reconfiguring a workstation from scratch takes an average of 4 to 8 hours. During this time, the employee cannot work. Data not backed up to the cloud is permanently lost.
4. The client trust impact
If a client’s data is compromised following the theft, you must notify them. The trust relationship built over years can collapse in a single conversation.
Why it happens — and how to prevent it
Company laptop theft most commonly occurs in three situations:
- Unattended offices in the evening or at weekends, in poorly secured premises
- Company vehicles: the laptop left on the passenger seat, visible from outside
- Public spaces: café, coworking space, train station — a few seconds of inattention is enough
The response is not purely organisational. It is technical, and it must be prepared before the incident occurs.
What really protects your SME IT security
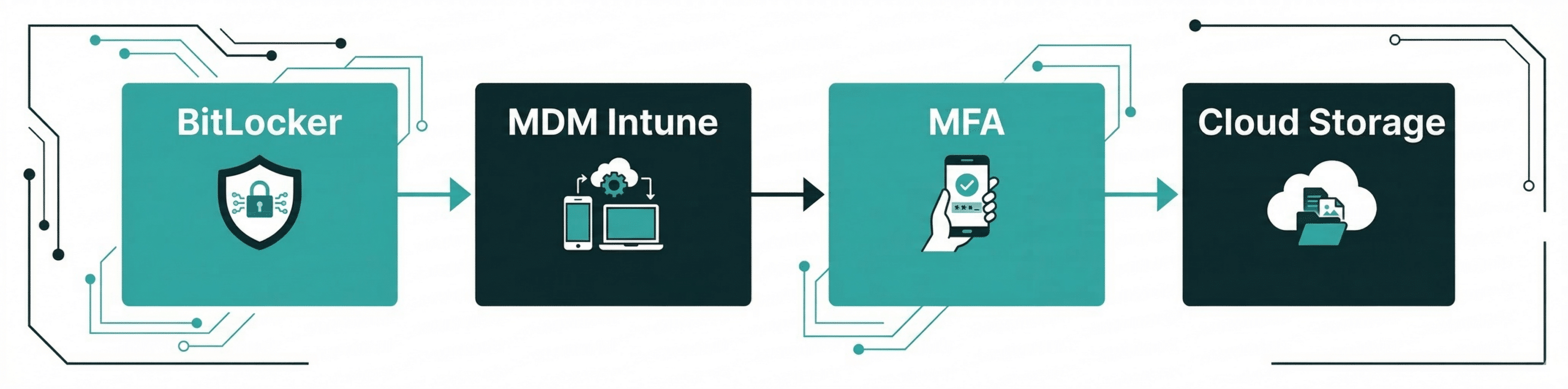
- BitLocker / FileVault — disk unreadable without password, even if physically extracted
- MDM (Intune / Jamf) — remote wipe or lock as soon as the device reconnects to the internet
- No-local-storage policy — sensitive data in M365/SharePoint, not on the disk
- MFA on all access — stolen credentials = door still blocked
- Documented revocation process — knowing in 5 minutes which accounts to cut, in what order
The golden rule of SME IT security in Dublin: it can’t be managed after the fact
The pattern we regularly see: a company suffers an incident, urgently looks for what it can do, and discovers it has no encryption, no MDM, and no documented access revocation process. The physical security of workstations must be designed — it cannot be improvised on the day of the theft.
5 questions to ask yourself today
Quick audit of your SME IT security — answer honestly:
- Are my laptops’ hard drives encrypted?
- Do I have a solution to remotely wipe a device if necessary?
- Do my employees use MFA on their email and cloud tools?
- If a company laptop was stolen tonight, would I know exactly which access to revoke and in what order?
- Is my critical data backed up, or only stored locally on workstations?
Let’s discuss your situation.
30 minutes, no obligation.
Let’s take a look together at what it would take to ease your IT workload. No sales pitch. Just an honest assessment of the situation.
Your IT architect. Your trusted partner.